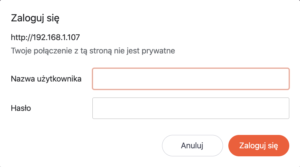
Basic authentication is one of the simples methods of providing credentials to access resources. Today I’m going to take a look on it and provide you with an example of a web page utilizing this mechanism written with PHP and Apache. How does basic authentication work? On request to a protected resource, the server sends […]